Refer to the exhibit.
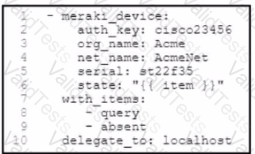
A security team observes an attack that originates from a Cisco Meraki device. To mitigate the attack, the team requests that the engineering team remove the /ice from the network. The security team also requests information about the device, such as Its name and location. Which tool must the engineering team use to meet the luirements by using tasks?
Submit