In which of the following incident handling and response stages, the root cause of the incident must be found from the forensic results?
Which of the following process refers to the discarding of the packets at the routing level without informing the source that the data did not reach its intended recipient?
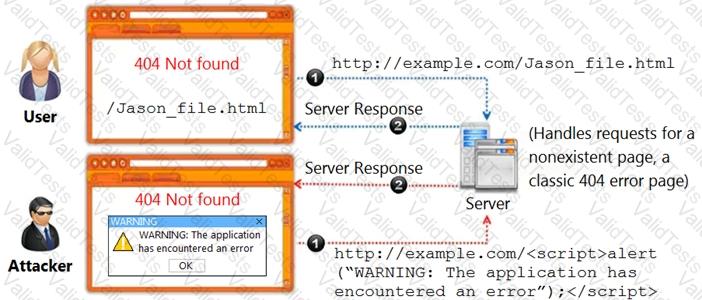
Identify the type of attack, an attacker is attempting on www.example.com website.
Which of the following framework describes the essential characteristics of an organization's security engineering process that must exist to ensure good security engineering?
An attacker exploits the logic validation mechanisms of an e-commerce website. He successfully purchases a product worth $100 for $10 by modifying the URL exchanged between the client and the server.
Original URL: http://www.buyonline.com/product.aspx?profile=12 &debit=100 Modified URL: http://www.buyonline.com/product.aspx?profile=12 &debit=10
Identify the attack depicted in the above scenario.
Harley is working as a SOC analyst with Powell Tech. Powell Inc. is using Internet Information Service (IIS) version 7.0 to host their website.
Where will Harley find the web server logs, if he wants to investigate them for any anomalies?
Where will you find the reputation IP database, if you want to monitor traffic from known bad IP reputation using OSSIM SIEM?
Chloe, a SOC analyst with Jake Tech, is checking Linux systems logs. She is investigating files at /var/log/ wtmp.
What Chloe is looking at?
Which of the following formula is used to calculate the EPS of the organization?
What does HTTPS Status code 403 represents?