In Linux OS, different log files hold different information, which help the investigators to analyze various issues during a security incident. What information can the investigators obtain from the log file
var/log/dmesg?
Rusty, a computer forensics apprentice, uses the command nbtstat –c while analyzing the network information in a suspect system. What information is he looking for?
You are asked to build a forensic lab and your manager has specifically informed you to use copper for lining the walls, ceilings, and floor. What is the main purpose of lining the walls, ceilings, and floor with copper?
Which of the following email headers specifies an address for mailer-generated errors, like "no such user" bounce messages, to go to (instead of the sender's address)?
Which of the following does not describe the type of data density on a hard disk?
Jacob is a computer forensics investigator with over 10 years of experience in investigations and has written over 50 articles on computer forensics. He has been called upon as a qualified witness to testify the accuracy and integrity of the technical log files gathered in an investigation into computer fraud. What is the term used for Jacob’s testimony in this case?
Which of the following file system uses Master File Table (MFT) database to store information about every file and directory on a volume?
What is the location of a Protective MBR in a GPT disk layout?
Which component in the hard disk moves over the platter to read and write information?
Tasklist command displays a list of applications and services with their Process ID (PID) for all tasks running on either a local or a remote computer. Which of the following tasklist commands provides information about the listed processes, including the image name, PID, name, and number of the session for the process?
In a Linux-based system, what does the command “Last -F” display?
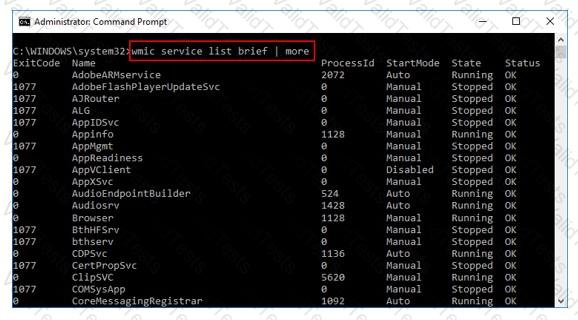
What is the investigator trying to view by issuing the command displayed in the following screenshot?
Which of the following is a precomputed table containing word lists like dictionary files and brute force lists and their hash values?
Which program uses different techniques to conceal a malware's code, thereby making it difficult for security mechanisms to detect or remove it?
What must an attorney do first before you are called to testify as an expert?