Which of the following techniques can be used to beat steganography?
Which of the following is a record of the characteristics of a file system, including its size, the block size, the empty and the filled blocks and their respective counts, the size and location of the inode tables, the disk block map and usage information, and the size of the block groups?
Which MySQL log file contains information on server start and stop?
An expert witness is a __________________ who is normally appointed by a party to assist the formulation and preparation of a party’s claim or defense.
You have been called in to help with an investigation of an alleged network intrusion. After questioning the members of the company IT department, you search through the server log files to find any trace of the intrusion. After that you decide to telnet into one of the company routers to see if there is any evidence to be found. While connected to the router, you see some unusual activity and believe that the attackers are currently connected to that router. You start up an ethereal session to begin capturing traffic on the router that could be used in the investigation. At what layer of the OSI model are you monitoring while watching traffic to and from the router?
What technique used by Encase makes it virtually impossible to tamper with evidence once it has been acquired?
Which of the following reports are delivered under oath to a board of directors/managers/panel of the jury?
Your company's network just finished going through a SAS 70 audit. This audit reported that overall, your network is secure, but there are some areas that needs improvement. The major area was SNMP security. The audit company recommended turning off SNMP, but that is not an option since you have so many remote nodes to keep track of. What step could you take to help secure SNMP on your network?
Which of the following files gives information about the client sync sessions in Google Drive on Windows?
Files stored in the Recycle Bin in its physical location are renamed as Dxy.ext, where “x” represents the ___________________.
Which password cracking technique uses every possible combination of character sets?
This type of testimony is presented by someone who does the actual fieldwork and does not offer a view in court.
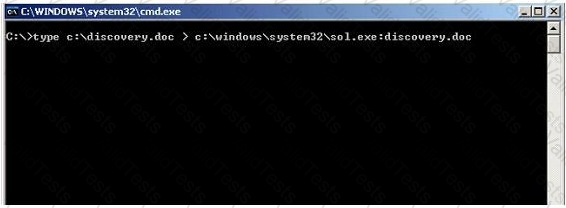
What feature of Windows is the following command trying to utilize?
What is considered a grant of a property right given to an individual who discovers or invents a new machine, process, useful composition of matter or manufacture?
Which of the following technique creates a replica of an evidence media?