Perspective clients want to see sample reports from previous penetration tests.
What should you do next?
What is the way to decide how a packet will move from an untrusted outside host to a protected inside that is behind a firewall, which permits the hacker to determine which ports are open and if the packets can pass through the packet-filtering of the firewall?
You've just been hired to perform a pen test on an organization that has been subjected to a large-scale attack. The CIO is concerned with mitigating threats and vulnerabilities to totally eliminate risk.
What is one of the first things you should do when given the job?
What attack is used to crack passwords by using a precomputed table of hashed passwords?
Suppose you’ve gained access to your client’s hybrid network. On which port should you listen to in order to know which Microsoft Windows workstations has its file sharing enabled?
Which of the following command line switch would you use for OS detection in Nmap?
This TCP flag instructs the sending system to transmit all buffered data immediately.
It has been reported to you that someone has caused an information spillage on their computer. You go to the computer, disconnect it from the network, remove the keyboard and mouse, and power it down. What step in incident handling did you just complete?
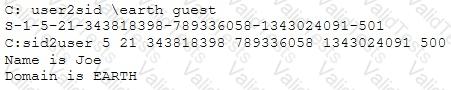
What did the following commands determine?
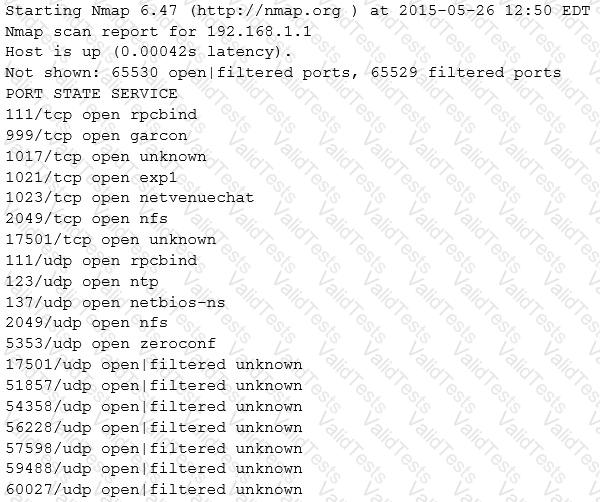
Which of the following Nmap commands will produce the following output?
Output: