The Alliance Web Platform Administrator uses both the GUI and command line to perform configuration and monitoring tasks on AWP SE.

Which operator session flows are expected to be protected in terms of confidentiality and integrity? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
What is the purpose of a SWIFT HSM? (Select the correct answer)
•Connectivity
•Generic
•Products Cloud
•Products OnPrem
•Security
An application only uses (i) the SWIFT API for reporting and gpi basic tracker calls through (ii) a tailored account not allowing business transactions management. Is this application in scope of the CSCF? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
In an entity having a small infrastructure and only 2 operators, the HR manager explains in a short interview how the security training is implemented providing one example. Would it be acceptable?

The Physical Security control also includes a regular review of physical access lists of the SWIFT-related servers' locations.
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
A Swift user uses an application integrating a sFTP client to push files to a service bureau sFTP server What architecture type is the Swift user? (Choose all that apply.)

A Treasury Management System (TMS) application is installed on the same machine as the customer connector (such as MQ server) connecting towards a Service Bureau Are these applications/systems in scope of CSCF?

Which of the following statements best describes the difference between an audit and an assessment as per SWIFT CSP definitions? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
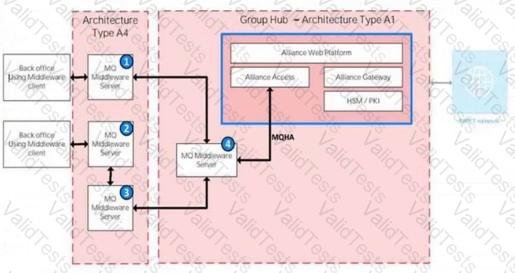
In the illustration, identify the component type of each of the numbered components.