How can rainbow tables be defeated?
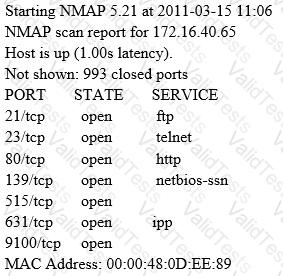
A penetration tester is conducting a port scan on a specific host. The tester found several ports opened that were confusing in concluding the Operating System (OS) version installed. Considering the NMAP result below, which of the following is likely to be installed on the target machine by the OS?
A covert channel is a channel that
Which results will be returned with the following Google search query?
site:target.com -site:Marketing.target.com accounting
Which security control role does encryption meet?
Which of the following is a detective control?
Which of the following is an application that requires a host application for replication?
A large company intends to use Blackberry for corporate mobile phones and a security analyst is assigned to evaluate the possible threats. The analyst will use the Blackjacking attack method to demonstrate how an attacker could circumvent perimeter defenses and gain access to the corporate network. What tool should the analyst use to perform a Blackjacking attack?
Which of the following programs is usually targeted at Microsoft Office products?
Which statement is TRUE regarding network firewalls preventing Web Application attacks?