What is the purpose of service rules in ClearPass? )
What happens when a client successfully authenticates but does not match any Enforcement Policy rules?
Refer to the Endpoint in the screenshot.
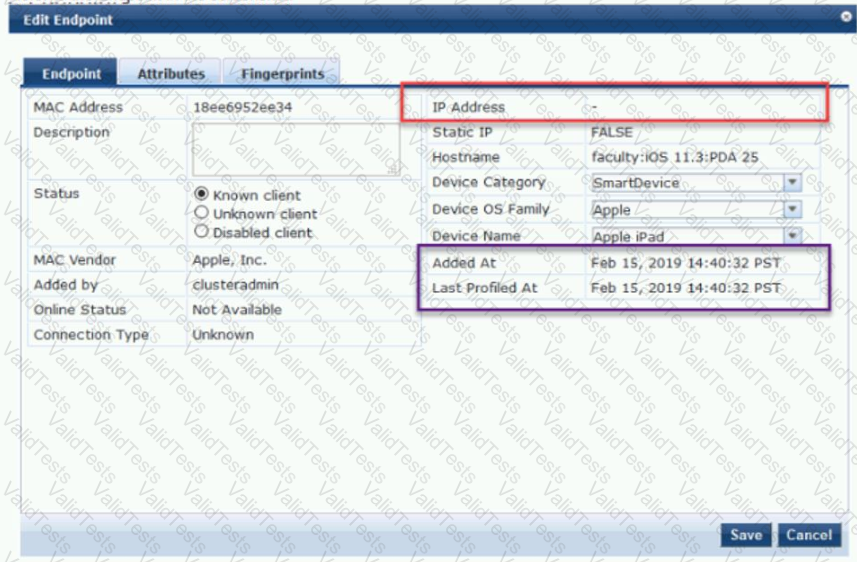
What are possible ways that it was profiled? (Select two)
Select all that apply
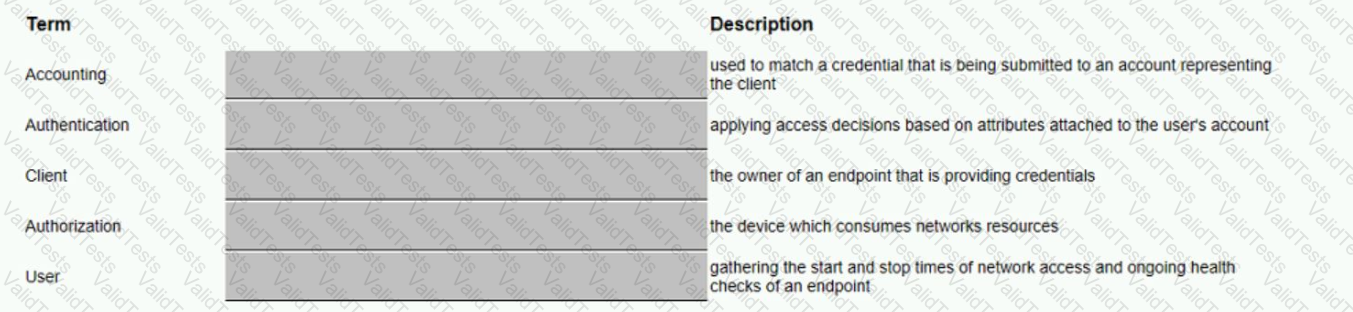
Match the security description to the term that best fits. Options are used only once.
Refer to the exhibit.
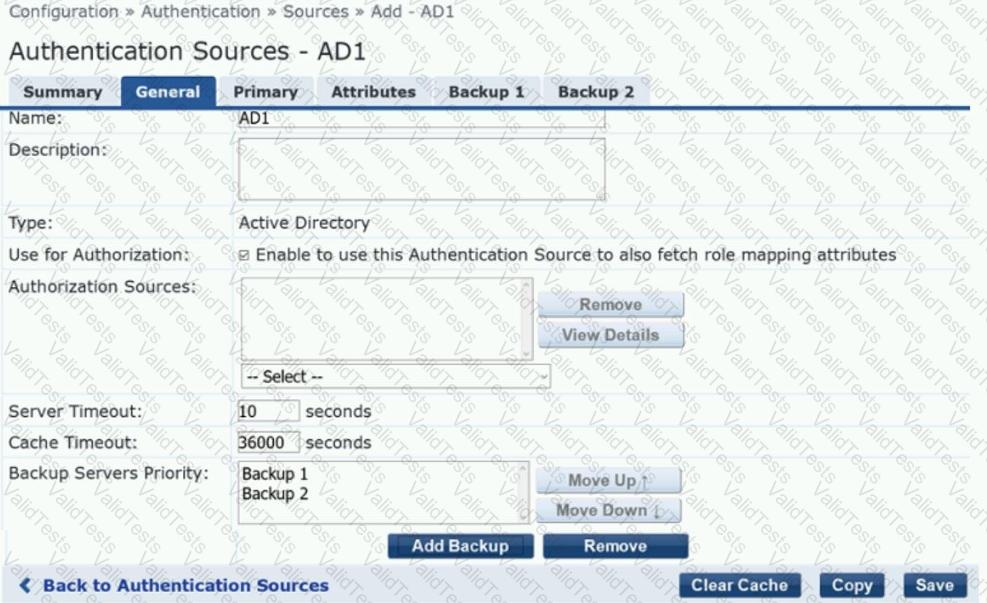
What are two consequences of the Cache Timeout being set to 36000 seconds? (Select two.)
Refer to the exhibit.
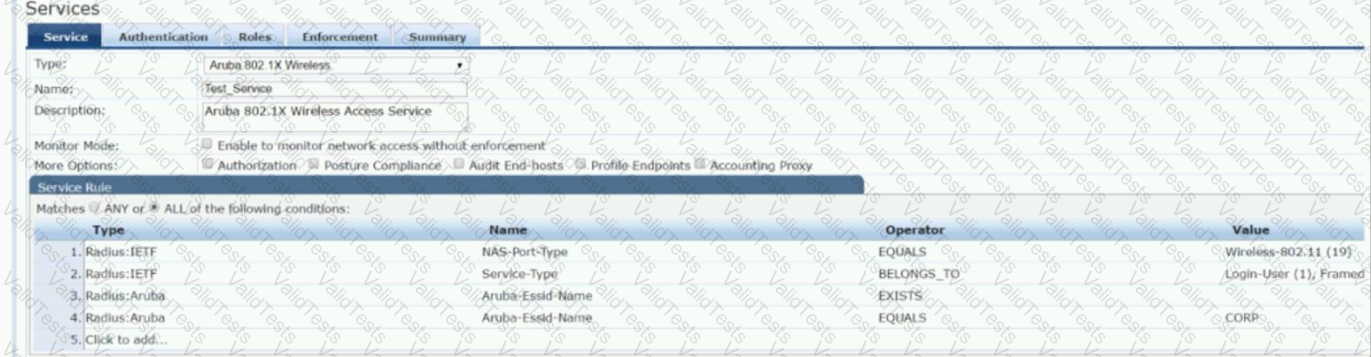
Which user authentication request will match the service rules of the Policy Service shown?
Which fingerprint collectors can help to distinguish between an iPhone and an iPad? (Select two.)
What is a good collector type used for ClearPass to discover devices with static IP addresses?