Which of the following statements is true about the incoming traffic in the firewall virtualsystem?(Select All that Apply)
Predefined URL categories on Huawei firewalls reside in the URL category database delivered with the device and do not need to be manually loaded.
: 52 DRAG DROP
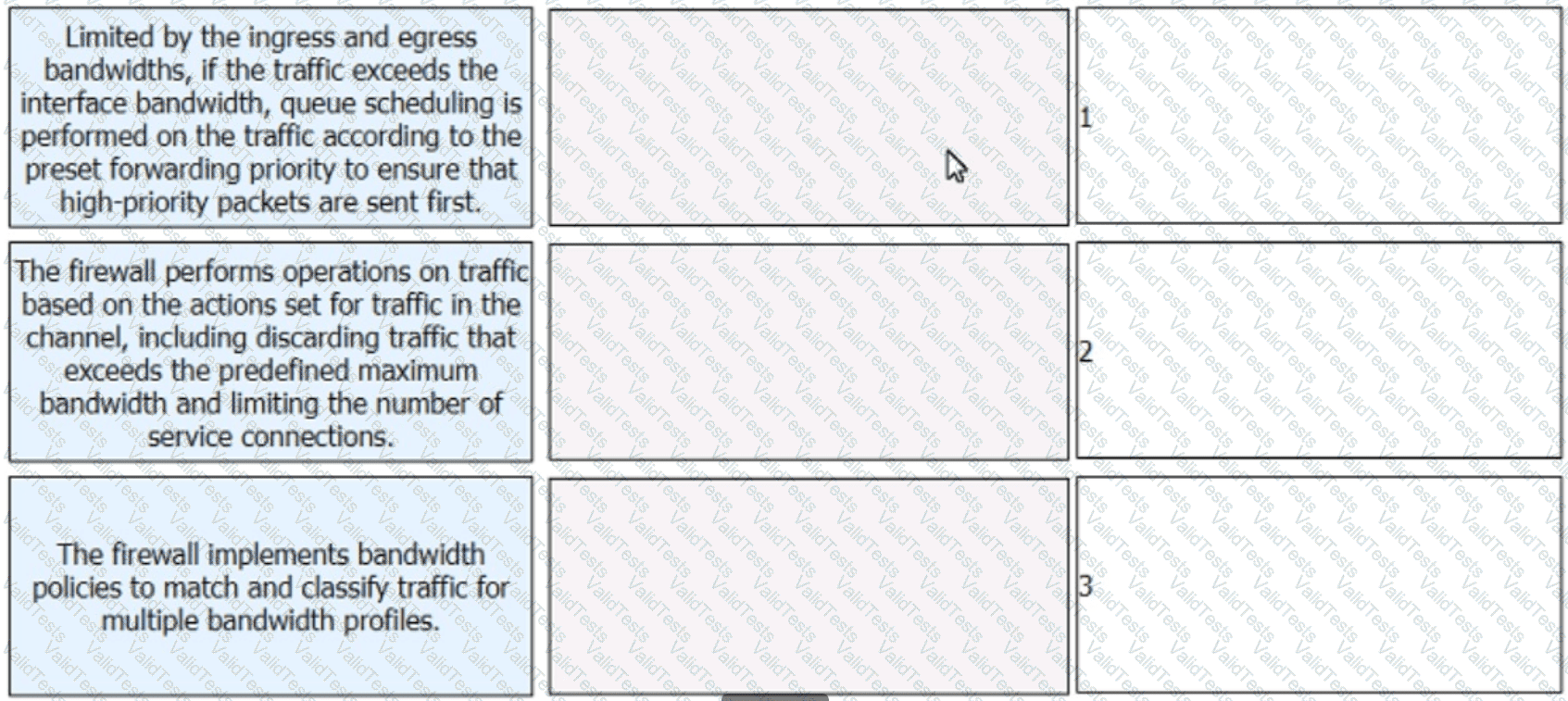
Arrange the steps of the bandwidth management process on firewalls in the correct sequence.
HWTACACS is a centralized information exchange protocol based on the client/server structure. It uses UDP for transmission and performs authentication, authorization, and accounting for users accessing the Internet through Point-to-Point Protocol (PPP) or Virtual Private Dial-up Network (VPDN) and administrative users logging in to devices.
iMaster NCE-Campus has a built-in LDAP module that enables it to function as an LDAP server to interconnect with access devices through LDAP.
Which of the following is not a process for remote users to access intranet resources through SSL VPN?
Trojan horses may disclose sensitive information of victims or even remotely manipulate victims' hosts, causing serious harm. Which of the following are the transmission modes of Trojan horses?(Select All that Apply)
Which of the following statements is false about health check?