During the implementation of iMaster NCE-Campus Wi-Fi location-based services (LBS), terminal location data is sent to an LBS platform through HTTP requests. Which of the following data formats is used in such HTTP requests?
SSH connections are usually established based on TCP/IP connections. In specific cases, SSH connections can be established based on UDP connections.
Exhibit:
A loop occurs because Spanning Tree Protocol (STP) is not enabled on the network. Which of the following symptoms may occur?
Which of the following statements about IPSG is incorrect?
The following information is displayed during OSPF troubleshooting. Based on this information, which of the following is the cause of the failure in establishing an OSPF adjacency relationship?
OSPF Process 1 with Router ID 10.0.12.2
OSPF error statistics
Interface: GigabitEthernet0/0/0 (10.0.12.2)
General packet errors:
0 : Bad version 0 : Bad checksum
0 : Bad area id 0 : Bad authentication type
0 : Bad authentication key 0 : Unknown neighbor
0 : Bad net segment 0 : Extern option mismatch
0 : Router id confusion
HELLO packet errors:
2 : Netmask mismatch 0 : Hello timer mismatch
0 : Dead timer mismatch 0 : Invalid Source Address
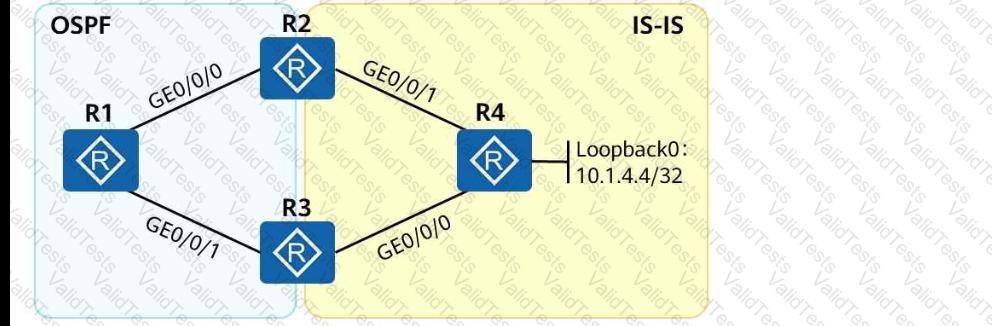
As shown in the following figure, an engineer tests network interconnection between two branches. To implement network interconnection,OSPFis deployed onR1, R2, and R3of branch 1, andIS-ISis deployed onR2, R3, and R4of branch 2. Which of the following operations needs to be performed to allowR1 to access R4's loopback interface address?
The RR (Route Reflector) is critical to the Huawei SD-WAN Solution, and its deployment mode varies based on the scenario. In which of the following modes can an RR be deployed?
In an MPLS VPN network, two-layer MPLS labels are added into data packets before they are transmitted over the public network. Which of the following statements regarding data packet processing are correct?
On a CloudCampus virtualized campus network, virtual networks are defined based on services. Each virtual network corresponds to a service, and isolation needs to be manually configured between virtual networks.
What can be determined from the following figure?
< R1 > display ipv6 routing-table protocol isis
Public Routing Table : ISIS
Summary Count: 6
ISIS Routing Table ' s Status : < Active >
Summary Count: 6
Destination : 3000:FDEA::4
NextHop : FE80::2E0:FCFF:FE98:2577
Cost : 20
Interface : GigabitEthernet0/0/1
PrefixLength : 128
Preference : 15
Protocol : ISIS-L2
Flags : D