You are asked to establish a hub-and-spoke IPsec VPN using an SRX Series device as the hub. All of the spoke devices are third-party devices.
Which statement is correct in this scenario?
Click the Exhibit button.
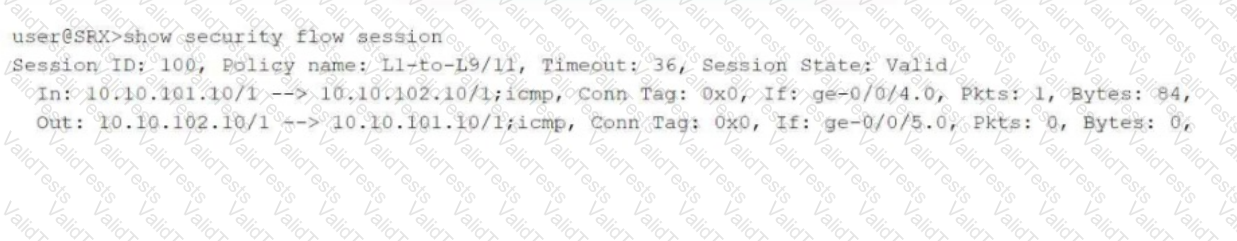
Referring to the exhibit, which two statements are true? (Choose two.)
You are asked to create multiple virtual routers using a single SRX Series device. You must ensure that each virtual router maintains a unique copy of the routing protocol daemon (RPD) process.
Which solution will accomplish this task?
Exhibit:
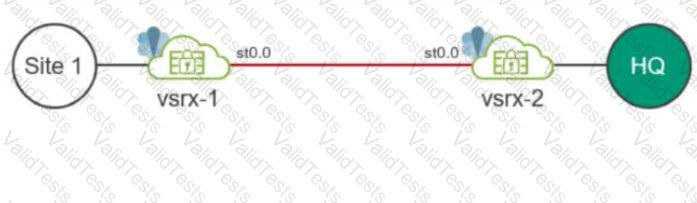
Your company uses SRX Series devices to establish an IPsec VPN that connects Site-1 and the HQ networks. You want VoIP traffic to receive priority over data traffic when it is forwarded across the VPN.
Which three actions should you perform in this scenario? (Choose three.)
You have a multinode HA default mode deployment and the ICL is down.
In this scenario, what are two ways that the SRX Series devices verify the activeness of their peers? (Choose two.)
Referring to the exhibit, you are assigned the tenantSYS1 user credentials on an SRX series
device.
In this scenario, which two statements are correct? (Choose two.)
Referring to the exhibit, you are attempting to set up a remote access VPN on your SRX series devices.
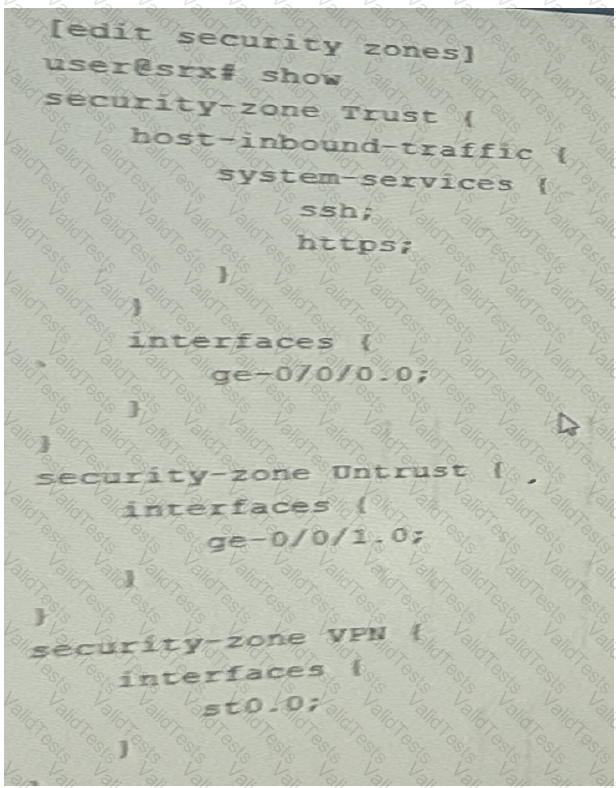
However you are unsure of which system services you should allow and in which zones they should be allowed to correctly finish the remote access VPN configuration
Which two statements are correct? (Choose two.)
Exhibit:
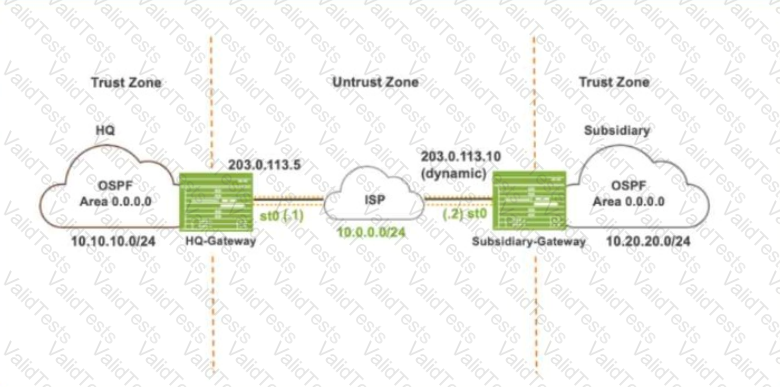
Referring to the exhibit, which IKE mode will be configured on the HQ-Gateway and Subsidiary-Gateway?
You want to configure the SRX Series device to map two peer interfaces together and ensure that there is no switching or routing lookup to forward traffic.
Which feature on the SRX Series device is used to accomplish this task?
You are configuring advanced policy-based routing. You have created a static route with next
hop of an interface in your inet.0 routing table
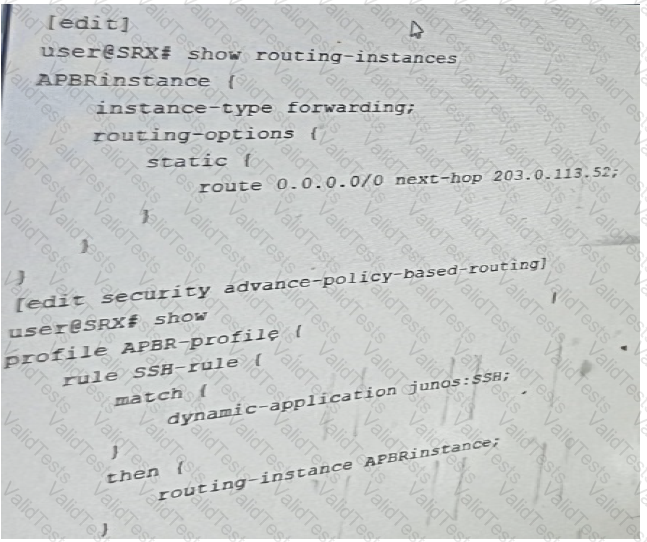
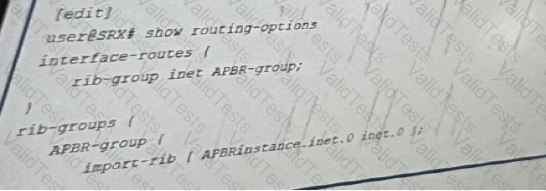
Referring to the exhibit, what should be changed to solve this issue?