If a “ping”-packet is dropped by FW1 Policy –on how many inspection Points do you see this packet in “fw monitor”?
Alice works for a big security outsourcing provider company and as she receives a lot of change requests per day she wants to use for scripting daily (asks the API services from Check Point fof the Management API. Firstly she needs to be aware if the API services are running for the management. Which of the following Check Point Command is true:
Which one is not a valid upgrade method to R81.20?
Vanessa is expecting a very important Security Report. The Document should be sent as an attachment via e-mail. An e-mail with Security_report.pdf file was delivered to her e-mail inbox. When she opened the PDF file, she noticed that the file is basically empty and only few lines of text are in it. The report is missing some graphs, tables and links.
Which component of SandBlast protection is her company using on a Gateway?
What is the command to check the status of Check Point processes?
Which of the following is a task of the CPD process?
Which statement is WRONG regarding the usage of the Central Deployment in SmartConsole?
Which command shows the current Security Gateway Firewall chain?
In Threat Prevention, you can create new or clone profiles but you CANNOT change the out-of-the-box profiles of:
How can you switch the active log file?
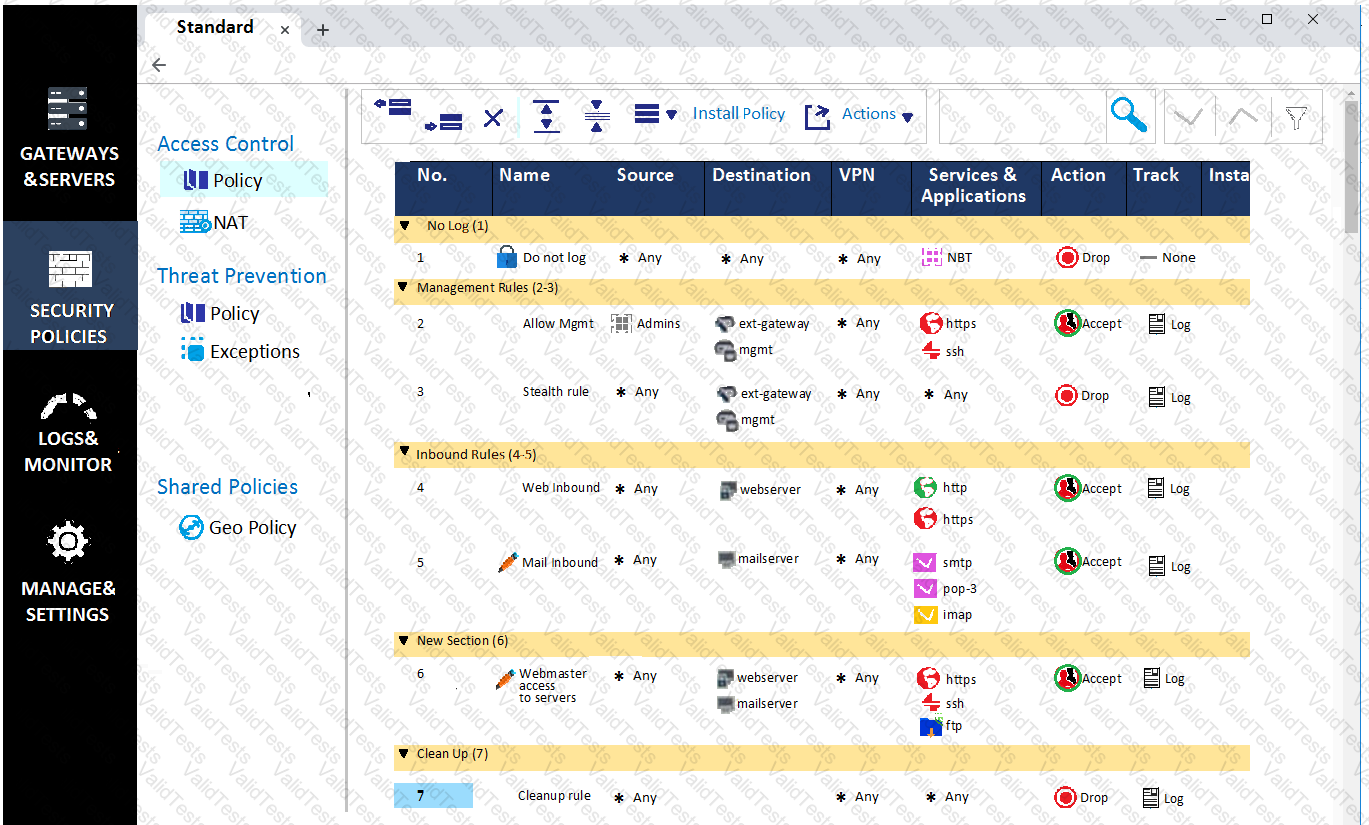
What can we infer about the recent changes made to the Rule Base?
What feature allows Remote-access VPN users to access resources across a site-to-site VPN tunnel?
Which component is NOT required to communicate with the Web Services API?
Main Mode in IKEv1 uses how many packages for negotiation?
Which command shows only the table names of all kernel tables?