Please order the following steps in the PKI life cycle correctly, 1. Issued, 2. storage, 3. Update, 4. verify[fill in the blank]*
Which of the following descriptions about the main implementation of single sign-on is wrong? ( )[Multiple choice]*
The following description of asymmetric encryption algorithms, which item is wrong?
In the automatic backup mode of hot standby on the second machine, which of the following sessions is backed up?
Regarding the characteristics of the routing table, which of the following items is described correctly
Which of the following is not included in the Business Impact Analysis (BIA).
Which of the following statements are correct about SYN flood attack defense technologies on Huawei firewalls?
An engineer needs to back up the firewall configuration. Now he wants to use a command to view all the current configurations of the firewall. May I ask the command he uses is ____[fill in the blank]*
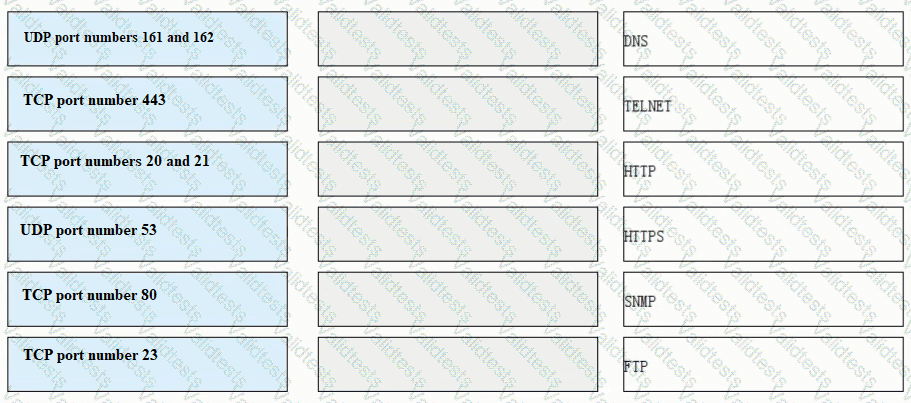
Match each of the following application layer service protocols with the correct transport layer protocols and port numbers.
When the Layer 2 switch receives a unicast frame and the MAC address table entry of the switch is empty, the switch discards the unicast frame.