Huawei Firewall only supports the inter-domain persistent connection function for TCP packets.
What is the protocol number of the GRE protocol?
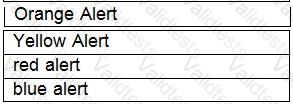
Drag the warning level of the network security emergency response on the left into the box on the right, and arrange it from top to bottom in order of severity.[fill in the blank]*
Which of the following is not included in the Business Impact Analysis (BIA).
Which of the following descriptions about the main implementation of single sign-on is wrong?
Which of the following problems cannot be solved using PKI?
Which of the following statements is incorrect about PKI?
Which of the following statements are correct about the PKI system structure?
Data monitoring can be divided into two types: active analysis and passive acquisition.
In the automatic backup mode of hot standby on the second machine, which of the following sessions is backed up?