On an IS-IS network, the length and components of aNETare the same as those of anNSAP. Which of the followingNETfields is used to uniquely identify a host or router in an area?
On the OSPF network shown in the figure, an adjacency has been established between R1 and R2. An engineer configures the commands in the figure on R2. In this case, which of the following routing entries may exist in the routing table of R2?
Compared with STP, RSTP defines the different port states. Which of the following statements regarding discarding and learning states are true?
A switch running a later IGMP version can identify Report messages of an earlier IGMP version, but the switch running an earlier IGMP version cannot identify Report messages of a later IGMP version. To ensure that IGMP runs properly, you are advised to set the IGMP version on the switch to be the same as or later than the IGMP version of member hosts.
In BGP, the origin attribute of the routes imported using the import-route command is incomplete.
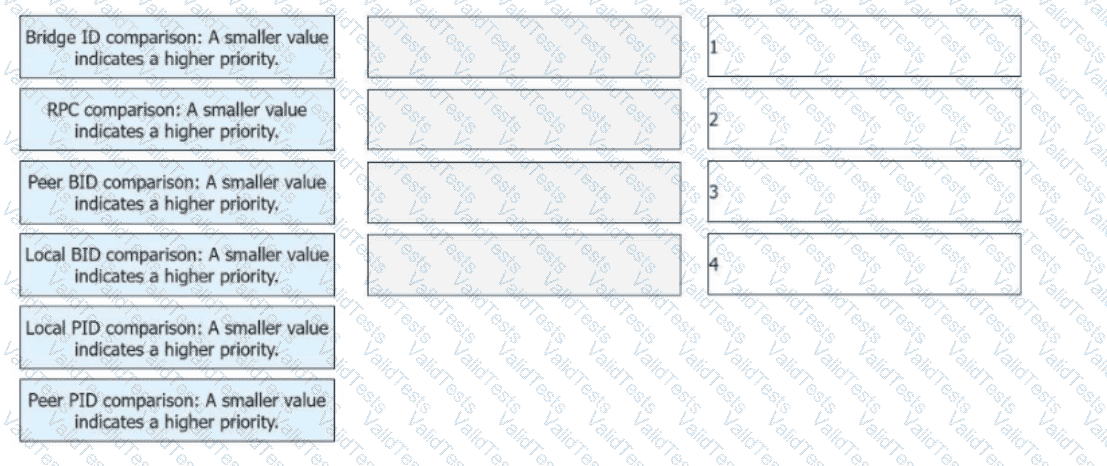
On an STP network, the root bridge, root port, and designated port are elected in sequence. The election rules of these ports are different. List the steps for electing the root port in sequence.
On an enterprise network, the directly connected interfaces of two OSPF routers are on different network segments and have different masks. To establish an OSPF neighbor relationship between the two interfaces, you can change their network types to which of the following?
The following figure shows acampus network. IS-IS is configured on all routers, and the network runs normally.
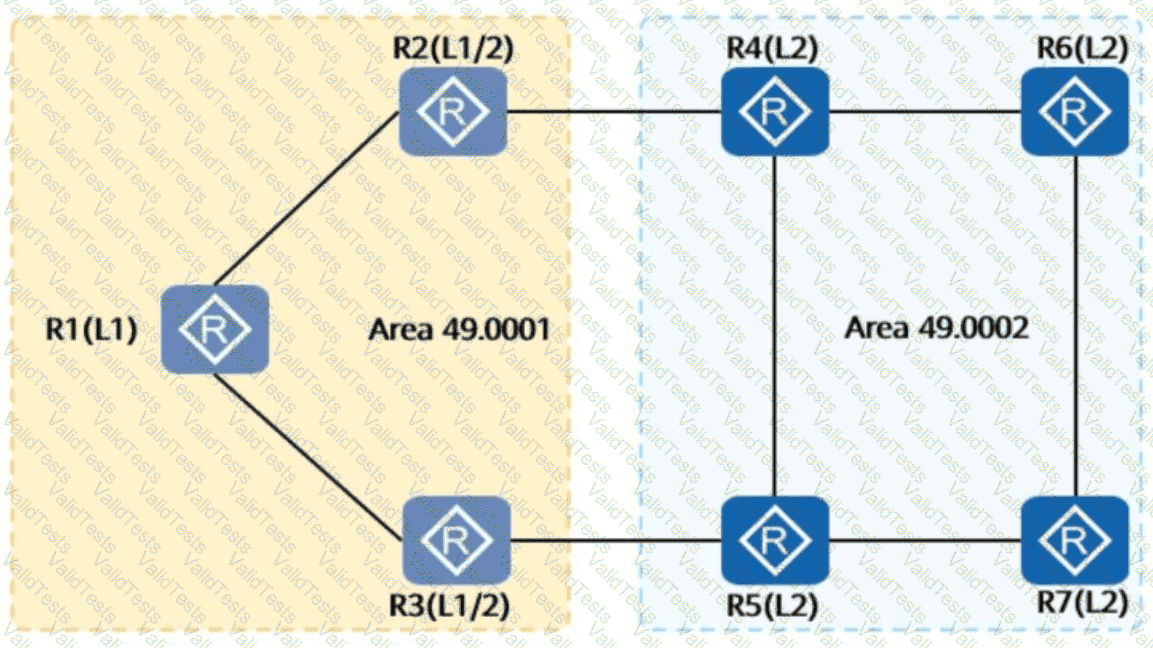
By default, which of the following routers havespecific routeson the entire network?
When an SSH client accesses an SSH server for the first time and the SSH server's public key is not configured on the SSH client, you can enable first-time authentication on the SSH client. This allows the SSH client to access the SSH server and saves the SSH server's public key on the SSH client. In this way, the next time the SSH client accesses the SSH server, the SSH client can use the saved public key to authenticate the SSH server.
OSPF neighbors have multiple states, such as Down, Init, 2-way, Loading, or Full. In which of the following states do OSPF routers negotiate the master and slave roles?