A company has a multi-tier web application. In the web tier, all the servers are in private subnets inside a VPC. The development team wants to make changes to the application that requires access to Amazon S3.
What should be done to accomplish this?
A company's application running on Amazon EC2 Linux recently crashed because it ran out ot available memory. Management wants to be alerted if this ever happens again. Which combination of steps will accomplish this? (Select TWO.)
A SysOps Administrator is deploying a legacy web application on AWS. The application has four Amazon EC2 instances behind Classic Load Balancer and stores data in an Amazon RDS instance. The legacy application has known vulnerabilities to SQL injection attacks, but the application code is no longer available to update.
What cost-effective configuration change should the Administrator make to migrate the risk of SQL injection attacks?
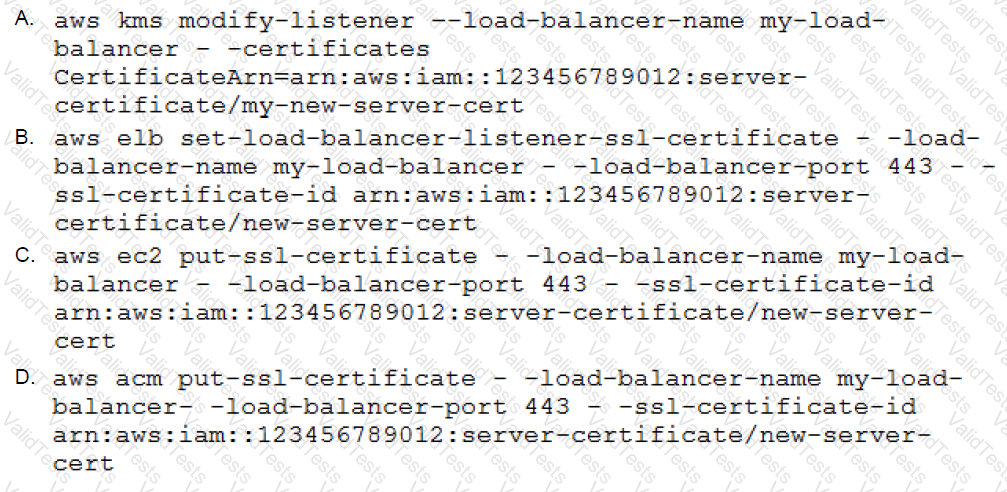
A SysOps Administrator has been able to consolidate multiple, secure websites onto a single server, and each site is running on a different port. The Administrator now wants to start a duplicate server in a second Availability Zone and put both behind a load balancer for high availability.
What would be the command line necessary to deploy one of the sites’ certificates to the load balancer?
A sysops administrator is writing an AWS Cloud Formation template. The template will create a new Amazon S3 bucket and copy objects from an existing Amazon S3 bucket into the new bucket. The objects include data files, images, and scripts.
How should the CIoudFormation template be configured to perform this copy operation?
A SysOps Administrator at an ecommerce company discovers that several 404 errors are being sent to one IP address every minute. The Administrator suspects a bot is collecting information about products listed on the company’s website.
Which service should be used to block this suspected malicious activity?
A SysOps Administrator is responsible for maintaining an Amazo EC2 instance that acts as a bastion host. The Administrator can sucessfully connect to the instance using SSH, but attempts to ping the instance result in a timeout.
What is one reason for the issue?
A sysops administrator must monitor a fleet of Amazon EC2 Linux instances with the constraint that no agents be installed. The sysops administrator chooses Amazon CloudWatch as the monitoring tool.
Which metric can be measured given the constraints? (Select Three)
A company is planning to expand into an additional AWS region for disaster recovery purposes. the company uses AWS CloudFormation, and its infrastructure is well-defined as code. The company would like to reuse as much of its existing code as possible when deploying resources to additional Regions.
A SysOps Administrator is reviewing how Amazon Machine Images (AMIs) are selected in AWS CloudFormation, but is having trouble making the same stack work in the new Region.
Which action would make it easier to manage multiple Regions?
A SysOps administrator maintains several Amazon EC2 instances that do not have access to the public internet. To patch operating systems, the instances should not be reachable from the Public internet.
The administrator deploys a NAT instance, updates the security groups, and configures the appropriate routes within the route table. However, the instances are still unable to reach the internet.
What should be done to resolve the issue?